Telecommunication security is of utmost importance in the digital age, where data and privacy are increasingly at risk. Here are some key aspects and measures to consider for protecting data and privacy in telecommunication:
- Encryption: Encryption is a fundamental security measure that protects data during transmission. Strong encryption algorithms ensure that data is converted into unreadable ciphertext, making it secure against unauthorized access. Telecommunication systems should employ robust encryption protocols to safeguard sensitive information.
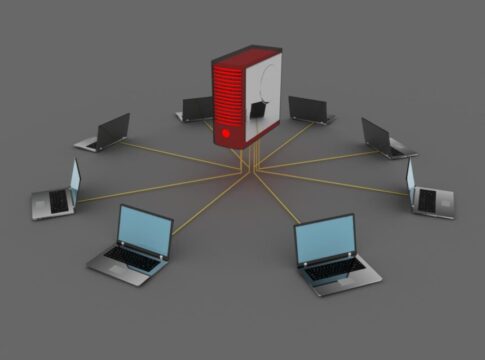
- Secure Network Infrastructure: Telecommunication companies should implement secure network infrastructure, including firewalls, intrusion detection systems, and secure routers and switches. These technologies help protect against unauthorized access, network attacks, and data breaches.
- Access Control: Access control mechanisms ensure that only authorized individuals can access sensitive information or network resources. Strong authentication methods, such as two-factor authentication, biometric authentication, and secure login credentials, should be implemented to prevent unauthorized access to telecommunication networks and systems.
- Network Monitoring: Continuous network monitoring is essential to detect and respond to potential security incidents promptly. Intrusion detection systems, network traffic analysis tools, and log monitoring systems can help identify abnormal activities, malicious attacks, or unauthorized access attempts. This allows for quick remediation and minimizes the impact of security breaches.
- User Privacy and Consent: Telecommunication companies must prioritize user privacy and obtain appropriate consent for collecting, storing, and using personal data. Transparent privacy policies should be in place, clearly outlining how user data is handled, protected, and shared. Consent should be obtained before collecting and using personal data, and users should have the option to control and manage their privacy settings.
- Data Protection Regulations: Telecommunication companies must comply with relevant data protection regulations, such as the General Data Protection Regulation (GDPR) in the European Union or the California Consumer Privacy Act (CCPA) in the United States. These regulations outline requirements for data protection, user consent, data breach notification, and user rights. Compliance with these regulations ensures that user data is handled securely and privacy rights are respected.
- Regular Security Audits and Assessments: Telecommunication companies should conduct regular security audits and assessments to identify vulnerabilities and ensure compliance with security best practices. Penetration testing, vulnerability scanning, and security assessments help identify weaknesses in the network infrastructure, applications, and systems, allowing for timely remediation.
- Employee Training and Awareness: Employees play a critical role in telecommunication security. Regular training and awareness programs should be conducted to educate employees about security best practices, safe browsing habits, phishing prevention, and incident reporting procedures. Employees should be aware of their responsibilities in safeguarding sensitive data and adhering to security protocols.
- Incident Response and Disaster Recovery: Telecommunication companies should have robust incident response plans and disaster recovery strategies in place. This includes procedures for identifying, responding to, and mitigating security incidents. Regular drills and testing of incident response plans ensure preparedness and enable swift and effective responses in case of a security breach or network outage.
- Collaboration with Security Experts: Telecommunication companies should collaborate with cybersecurity experts and industry partners to stay updated on emerging threats and security trends. Information sharing and collaboration within the industry help identify and address new security challenges effectively.
By implementing these security measures and adhering to best practices, telecommunication companies can protect data and privacy in the digital age. Prioritizing security not only safeguards sensitive information but also builds trust with customers, enhancing the overall reputation and reliability of telecommunication services.